Biometrics is the statistical and mathematical measurement of unique physical or biological characteristics for identification purposes. In the field of cybersecurity, the use of biometrics refers to the use of unique biological features, such as fingerprints, facial features, or iris patterns, for digital authentication and access control.
One of the main benefits of biometrics in cybersecurity is the high level of accuracy and reliability it provides. Unlike passwords and other forms of authentication that can be easily forgotten or stolen, biometric information is unique to each individual and is difficult to fake or forge. This makes it a powerful tool for protecting against unauthorized access to sensitive information and systems.
There are a number of different biometric technologies that are commonly used in cybersecurity, including:
- Fingerprint scanners: These devices use sensors to scan and analyze the unique patterns of an individual’s fingerprints. Fingerprint scanners are widely used for authentication and access control on a range of devices, including smartphones, laptops, and tablets.
- Facial recognition: This technology uses advanced algorithms to analyze and compare the unique characteristics of an individual’s facial features, such as the shape of their eyes, nose, and mouth. Facial recognition is used for a variety of purposes, including unlocking devices, accessing secure areas, and identifying individuals in security footage.
- Iris scanners: These devices use advanced
What is Biometrics?
It is seen in many institutions in our country nowadays, when entering through the door, one has to enter the screen of the device with a fingerprint.
The question may be why there are so many fingerprints. Studies have shown that every human being has some unique characteristics. Fingerprints, eye iris, DNA, and handprints are all naturally different for each person.
So these features are used to identify a person. Biometrics is the process of identifying individuals based on these unique human characteristics.
As a result of using biometrics, there is almost no opportunity to know the identity. Security measures that used to be based on a secret number or confidential information are now being phased out.
Biometrics is usually based on two types of information. One is the physical characteristics, such as fingerprints, iris, DNA, etc. The other is behavioral traits, such as pronunciation, type of signature, etc.
These features do not match one person to another. In addition to passports, ID cards, driving licenses, etc., biometrics are also used to keep track of the entry and exit of employees in the office, secure access to high-security places, and identify criminals.
Neighboring India has started using fingerprints on ATM machines to withdraw money from uneducated farmers. At present, our national identity cards have also been fingerprinted for parallelism.
Bioinformatics
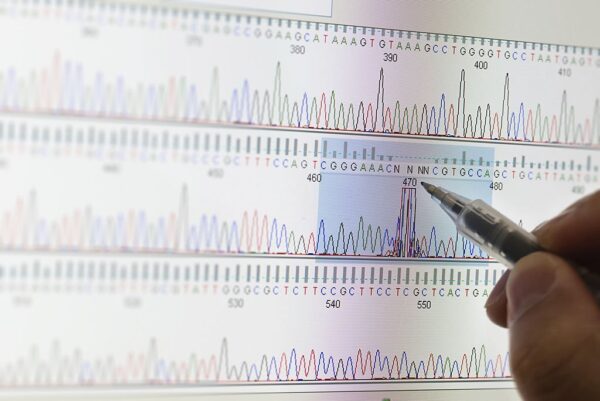
The biological world has been buzzing since the discovery of the DNA helix model by Watson and Crick. One after another research is being done on DNA, new mysteries are being revealed, a lot of unknown information is being discovered. This information is again related to one another. It is said that this information is doubling every 18 years.
A large amount of this information needs to be organized in such a way that it can be used in other future research. And there is nothing more efficient than a computer to store such information. Bioinformatics is a branch of technology that combines all the information of biology, microbiology, molecular biology, biochemistry, and genetics together in such a way that other research can be done later. Helps to give.
Bioinformatics reduces the labor and cost of researchers by several times. For example, let’s say an antidote to a virus needs to be developed. This may require research on thousands of peptides, of which only four will work.
But it is impossible, complex, and time-consuming to find out just four peptides by testing thousands of peptides in a laboratory.
In this case, using software to create artificial three-dimensional (3D) models, it is possible to distinguish roughly ten peptides by combining the structure of one with the structure of the other, which is capable of making vaccines. As a result, instead of thousands of peptides, only ten peptides diagnosed with software can be tested in the laboratory and those four peptides can be easily extracted.
Bioinformatics is not a single subject but a combination of many. Working in bioinformatics requires knowledge of computer science and engineering, mathematics, logic, and biological knowledge.
This is because of the simultaneous application of artificial intelligence software, complex algorithms, image processors, isolated mathematics, statistics, three-dimensional modeling software, etc.
The application of bioinformatics is seen in science fiction films. Even Spiderman’s latest film, released in 2013, shows the use of bioinformatics in the laboratory.
Genetic Engineering
It is often heard that the boy is like his father or the girl’s intelligence is like that of his mother. The question may be, how do parents transfer their possibilities? The answer to this question is that the branch of science that is discussed is called genetics. Genetic engineering began in 1972 with the discovery of recombinant DNA technology by Paul Berg.
In the most modern branch of biochemistry, life is defined at the molecular level, it is called The Molecular Logic of Life. Written in just four letters, A-T-C-G is called the Language of GOD. Genetic engineering deals with the creation of transgenic plants and animals. Of the term “genetic”
The reason for adding “engineering” at the end is that it is only in this branch of biology that you can customize the virus or bacteria of your choice, whichever comes your way. Undoubtedly, the most exciting thing for an investor is that something completely alive is working just like his design.
Other branches of biotechnology are Microbiology, Biochemistry, Biostatistics, Immunology, Organic Chemistry, Enzymology, Insilico (Computational) Biology, and Tissue Culture.
That is why a genetic engineer is simultaneously a microbiologist, biochemist, statistician, biochemist, and computer engineer. Because of the huge DNA review, he has to design the software starting by applying the statistics correctly.
The application of genetic engineering is affecting our agricultural, food, medical, and manufacturing systems. Artificially genetically modified advanced organisms are called transgenic organisms.
Research has shown that it is possible to produce transgenic cows that are more resistant to disease, grow faster, have faster milk quality, are more nutritious, and have several times more milk than normal cows.
Transgenic cow’s, goat’s and sheep’s milk have been used as sources of hormones such as insulin, blood clotting, and red blood cell production. Uniforms, medical equipment, tennis equipment, and even bio style are being made from transgenic goat’s milk fibers with the help of genetic engineering.
The field of great potential is this genetic engineering. In developed countries, thousands of new studies on genes are being conducted every day. Genes are also being researched in our country. The genetic design of jute and its parasitic fungi is considered to be one of the greatest discoveries ever made in Bangladesh.
The jute gene design was successfully unveiled in mid-2010 in a joint effort by a team of enterprising researchers from Dhaka University, Bangladesh Jute Research Institute, and Datasoft, an IT company led by Bangladeshi geneticist Dr. Maksudul Alam.
Not only that, under the leadership of scientist Maksudul Alam, so far, the scientists of Bangladesh have unveiled the secret of the life of 500 species of harmful fungi. Moreover, in early 2014, in a joint effort with Chinese scientists, our country’s scientists under the leadership of Dr. Moniruzzaman succeeded in unraveling the mystery of the life of the buffalo.
At present, many books written by some researchers in Bangladesh are being admired as textbooks of genetic engineering in different universities and laboratories of the country and abroad.
Nano Technology
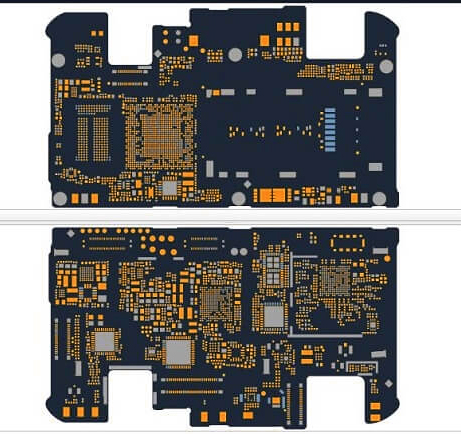
Nanotechnology (nanotechnology or nanotech for short) is the science of changing and controlling matter at the molecular level. Nanotechnology typically works with structures that are smaller than at least 100 nanometers in any one dimension. A fraction of a billionth of a meter is called a nanometer.
The size is so subtle that it is said that the nostrils of a human hand grow by one nanometer per second. Until the Second World War
The fineness of the instrument was measured on a millimeter scale. But after the end of World War II, a new era in science and technology began. The semiconductor began its journey.
And it all started with the invention of the transistor. This reduces the size of the equipment. As a result, thinking about the micrometer unit began. It can be said that the journey started with microtechnology.
After that, technology started advancing at a tremendous pace. Research began on how to make various items, such as televisions, radios, refrigerators, etc., smaller. How small a company is.
All these consumables could reach us, the competition began. And if everything is possible for the benefit of semiconductor technology. Early mobile phones were the size of radios.
But now mobile phones as thin as biscuits have arrived. There are also mobile phones now that can be bent at will. Maybe a lot more will come in the coming days.
There are two processes in nanotechnology, one is “top to bottom” and the other is “chi to top” (bottom to top). In the sub-bottom method, an object is cut down and given a specific shape.
And bottom-to-top is to make something big out of small things. Our current electronics is sub-chu bottom technology. And nanotechnology is the bottom-to-top technology.
Those who use computers know that the value of computers is declining every year. Every year cheaper and better working computers are available. In fact, this computer is related to nanotechnology.
The processor inside the computer, this processor has a number of tiny nanometer-scale circuits inside. And nanotechnology is being used in it. As a result, the size of the processor is constantly decreasing but the capacity is increasing several times
By Also the capacity of computers to store data on a hard disk is increasing day by day. Nanotechnology is also being used on hard disks. Now 1 terabyte hard disk is easily available in the market. But even ten years ago this thing was unimaginable.
Bangladeshi scientists are not far behind in the application and research of nanotechnology. A team of researchers led by expatriate Bangladeshi Professor Taher A Saif has developed a very small device called Machines of Micro Electro Mechanical Systems (MEMS). These are so small that they are smaller than human hair.
Microscopes are required. This device is especially used in cars, cameras, televisions, and computers. The laboratory also produces a variety of instruments smaller than 100 nanometers. Another Bangladeshi researcher is currently an associate professor in the Department of Electrical Engineering and Computer Science at the University of California, Berkeley, USA.
Sayif Salauddin has solved one of our most well-known problems using nanotechnology. Using the internet on a laptop or smartphone drains the battery quickly, a problem for all users. Also with the development of all other electronic devices, such as televisions, computers, watches, etc., the cost of electricity has also increased, which we often do not notice.
As a result, the demand for electricity is constantly increasing. People are also getting involved in expenses. Sayif Salauddin has given a solution to this problem by reducing the cost of electricity of electronic equipment by keeping the efficiency right.
For his groundbreaking invention, Sarif received the Nanotechnology Early Career Award in 2012 from the International Institute of Electrical and Electronics Engineers, the highest body of electrical engineering.
Ethics of ICT Usages
With the advancement of technology, its misuse is also increasing day by day. In the absence of human morality, with the power of technology, it is possible to cause great mental, economic, social, political, national, and even international damage which is a heinous crime.
1. Mental and social harm: With the help of technology, it is becoming possible to reach more people.
But without taking advantage of this opportunity, if someone is socially degraded, insulted, humiliated with the help of fake pictures or documents by using obscene language, then it is definitely a punishable offense. Many times anti-state and anti-people comments or mails are spread by cracking one’s online account, for which that person has to take the responsibility. Harassment of people by leaking confidential, personal information to the public is also an abuse of technology. There are many cases of suicide due to such crimes.
2. Economic loss: There have been many cases of people disappearing from their accounts with their bank account numbers, ATM numbers, passwords, etc. in the hope of false rewards in various fake emails. Many times money is demanded through mail showing false greed. Once you enter many sites you are asked to enter the account number and password to send millions of dollars won in the lottery. Danger if you step into such a trap. Unauthorized money can be lost by stealing, deleting, or injecting viruses into an individual or organization’s site or system by illegally entering or hacking them.
3. National and international losses: A country may have some confidential information that is necessary to establish its economy, trade, defense or diplomatic relations. If such information is smuggled to another country, it has the potential to provoke a war between the two countries. With the help of technology, crackers and spies from different countries try in various illegal ways to bring out this secret information of other countries. Later, the country has the advantage of exploiting this information for fear of leaking. Such unethical use of technology is highly reprehensible.
4. Security Disadvantages: Technology is used in all aspects of life in foreign countries, from security measures to traffic control. In such a system, various crimes can be committed by disabling the security system of those technologies. These crimes are termed as cyber crimes. The amount of damage in these cases is huge.
5. Pirated Software and Copyright: The software we use for various purposes. They are made by any person or organization. In most cases these softwares are made for the purpose of selling and doing business. But some unscrupulous people release these softwares by copying or piracy.
Because of the low price, people buy these guided software instead of the original software. As a result, programmers suffer financial losses and their talents are not properly evaluated. In many cases, the software designed by one person claims that the other person designed it himself.
Proper enforcement of copyright law is essential to protect intellectual property in these cases. The law against piracy in our country is very weak. As a result, software designers are not interested in working in our country. Because if there is no evaluation of one’s own work, then no one will be interested in making a software by working hard. This is why most of the software designing countries are in the western world. Because copyright laws are strictly adhered to in their country.
And severe punishment for piracy. On the other hand, in the South Asian region, no one has developed a big field of software design as these laws do not mean much. Now the question may come, what will those who cannot afford to buy original software at a higher price do? There is no such thing as always having to buy original software. Many original softwares are legally available for free on the Internet. These are called free software. Anyone can download and use this software for free from the internet.
Software such as Ubuntu as an operating system, Libra Office for writing, GIMP for photo editing, Eiscape for graphics work, Blender for 3D modeling, Mozilla Firefox for browsing the Internet and Google Chrome are available for free. Many people think that these free softwares are of low quality because they are available for free. The idea is completely wrong.
According to 2014 data, out of the top 500 supercomputers in the world, 481 supercomputers run on Linux. Linux itself is free software. It does not cost money to use. The Ubuntu operating system is also built with Linux. The fastest supercomputer among the first 500 supercomputers runs on the Ubuntu operating system. The most popular Android operating system currently used in smartphones is also built on Linux.
If it was inferior in quality, surely the Moons operating system would not be used in supercomputers or smartphones worldwide.
Ten guidelines on ethics in the use of information and technology
In 1992, the Institute of Computer Ethics provided ten guidelines for computer users on ethics in the use of information and technology. These are seen as a measure of the ethics of the use of information and technology. The instructions are:
1. Do not use computers to harm others
2. Not to interfere in the work of others
3. Not to collect information secretly from other files
4. Do not use any computer for theft
5. Do not use computers to prove false evidence
6. Do not use or copy free software for sale
7. Do not use other people’s computers without permission
8. Embezzling the deeds of others, not doing
9. Before designing software, think about its social impact
10. Always use the computer with due consideration and respect
These guidelines were first introduced by Ramon Barquin in his research paper entitled “In Pursuit of a Ten Commandments for Computer Ethics.”